What’s CylancePROTECT?
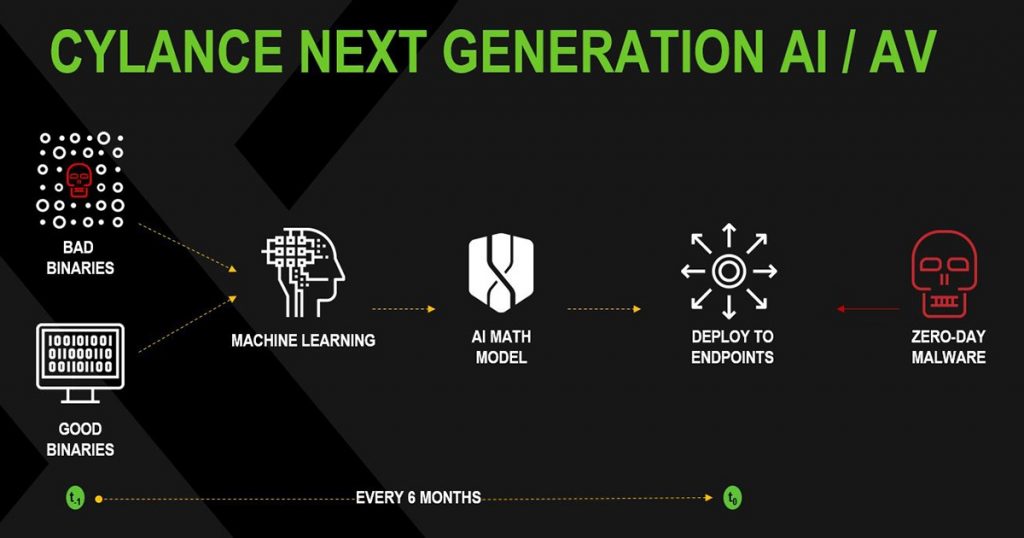
CylancePROTECT is a endpoint protection application from Cylance that finds, averts, and prevents safety dangers. With this program, organizations can secure their IT infrastructures protected from cyber threats, since the alternative comes with artificial intelligence that functions better in relation to those utilized by other anti virus programs. CylancePROTECT is an efficient line of defense against complex cybersecurity attack methods that attempt to hack a organization’s endpoints. Last, CylancePROTECT permits companies to have real-time assault avoidance. The program scans many files completely as it believes if they are secure, impartial, or even a flat-out threat into the machine.

Product Quality Score
| Product Quality Score | |
| Characteristics 8.5 | 8.7 TOTAL SCORE |
| Simplicity of use 8.7 | |
| Customer support 8.7 | |
| Value for money 8.9 |
CylancePROTECT features
Main characteristics of CylancePROTECT are:
- Autonomous Malware Execution Control
- Predictive Analysis
- PUP Rejection
- Malware Execution Prevention
- Device Binary Lockdown
- USB Storage Device Control
- Binary Modification Prevention
- Bad Binary Prevention
- Memory Misuse Protection
- Script Control
- Process Injection Freezing
- Memory Exploitation Protection
- Privilege Escalation Blockage
CylancePROTECT Benefits
The main advantages of all CylancePROTECT are its effective protection, user friendly interface, heavyweight functionality, and multi-faceted malware execution control. Here are CylancePROTECT’s benefits:
Effective Protection
Using CylancePROTECT, IT infrastructures are safe from cyber threats and does its job nicely. The program provides almost 100% malware execution denial irrespective of any strategy it does to this information. With this application, business data is protected from any attack as well as undesirable programs.
CylancePROTECT also packs an easy-to-use interface and doesn’t need expert training to use and manage. Daily endpoint management and signature updates are automatic which boosts security and reduces safety expenses.
Heavyweight Performance
CylancePROTECT might be a little program but it does a heavyweight work when it starts functioning. The app only uses approximately 1-3% of your computer’s processing power, which can be lesser than most security programs. Despite its small size, it makes up for the quality protection.
Multi-Faceted Malware Execution Control
As malware frequently attacks in different styles, CylancePROTECT has resources to intercept those malicious applications irrespective of their approach. Might it be via devices, programs, memory, or scripts, endpoints are secure from these attacks.

Technical Specifications
Devices Supported
Present
iOS
Android
Desktop
Client types
Small Company
Moderate business
Business
Support Forms
Telephone
Online
Customer Service
Telephone
Online
Pricing Strategies
CylancePROTECT pricing is available from the following strategies:
FREE TRIAL
QUOTE-BASED PLAN
Contact seller

Cyclane Pros and Cons
Advantage
“Cylance is simple to use and really does a wonderful job of protecting our endpoints. The behavior-based engine is quite a bit more accurate and responsive than conventional signature-based antivirus.”
“We now have a weekly conference call with all the seller implementation team who helps us understand how to administer the item and helps us install the policies and zones for our surroundings.”
“Cylance ensures each endpoint is fully shielded and allows easy whitelisting for whatever it gets too grabby with.”
“From the test phase to actually rolling out it I’ve been extremely pleased with our decision to choose Cylance. I rated everything 5 stars because I genuinely feel as they’ve made it.”
Disadvantages
“No reports of virus infection since we use this.”
“Sometimes difficult to tell if it is working, at times it blocks needed software and it is pain to permit it through.”
“Can be frustrating to constantly be handling the whitelist.”
“The program can block essential executables. While these may be whitelisted, it actually disrupts the workflow to prevent and need to update the whitelist and then push it to all apparatus.”

Conclusion:- CylancePROTECT is merely one of the ideal endpoint protection solutions now available on the business. The mix of features like simple management and supply, quite low hardware resource consumption and higher hazard detection/prevention capacity is definitely something tremendously sought by associations needing to get rid of malware.